Sinatra Promotions Guardian
How I led the design of a double-checking system to eliminate critical errors, implement a commercial governance layer, improve the auditing process and close the door to insider fraud in VTEX promotions and coupons. The e-commerce platform behind major LATAM retailers.
- Role
- Product Designer
- Team
- Product · Engineering
- Timeline
- 2025 Q1 -> Q2
- Platform
- Sinatra (VTEX)
- 0
- Promotions with errors reaching production within 90 days of launch
- 35%
- Of the enterprise teams at Sinatra adopted the feature in the first week
- 10s
- Average time to detect anomalous promotion with potential risk
- 100%
- Traceability of revisors and approvers across all active promotions.
VTEX doesn't record who creates a promotion.
VTEX is the e-commerce platform behind major LATAM retailers. At the core of these companies' commercial strategy are promotions: discounts, coupons, special conditions. The problem is that VTEX, by default, doesn't record who created a promotion.
Any user with access to the admin panel can log in, create a promotion, and log out. No trail. No review. No control.
Inside the Sinatra ecosystem — an AI Agents hub integrated with VTEX — we monitor commercial anomalies in real time. As we expanded our coverage, it became clear that the biggest risk wasn't only in the algorithms, but in the human processes around promotions.
VTEX's official audit exists, but requires opening a request and can take weeks or even months until it gets concluded.
In 2025, we detected an anomaly at a client with a suspicious pattern: a promotion with no minimum purchase value, no per-customer usage limit, and an 80% discount across an entire category. The promotion stayed live for hours before being noticed; dozens of orders went through, and thanks to the alert that was triggered, the damage was contained.
That case was the starting point for an investigation in which we uncovered a Product Governance failure.
No human review
Promotions went straight from creation to production with no second pair of eyes.
Frequent errors
~23% of monthly created promotions had configuration errors.
Slow and costly audits
Triggering a VTEX promotion creation audit took 4 to 8 weeks.
Three groups. Three realities. The same blind spot.
Before thinking about a solution, we needed to understand the different profiles living with this problem. We mapped three distinct groups and ran interviews and observation sessions over two weeks.

Marketing & Ops teams
Responsible for creating promotions. Manual process — spreadsheets, screenshots, WhatsApp with the manager. There's no official internal approval flow.
“We simply create the promotions that the manager authorizes via Email and send it to production when the campaing starts.”
Commercial managers
E-commerce heads and coordinators. There's no real-time visibility into which promotions are active and who created them.
Product & CS teams
Internal Product and Customer Success. Most issues came in through support, not through proactive alerts.
“I only find out when a client calls to complain. By then it's already too late.”
Insights
The approval process exists, but it's informal. Every team had some way of giving an "ok" before activating a promotion — always over WhatsApp or Slack. The system recorded none of it.
Internal fraud is the scenario that scares them most. "It happens more than you'd think" came up in more than one interview.
Three questions guided the exploration.
How might we turn the informal approval process into something traceable and part of the natural workflow?
How might we ensure no promotion reaches production without at least two pairs of eyes, without creating excessive friction?
How might we offer real-time audit traceability without depending on VTEX's slow processes?
Constraints that shaped the solution
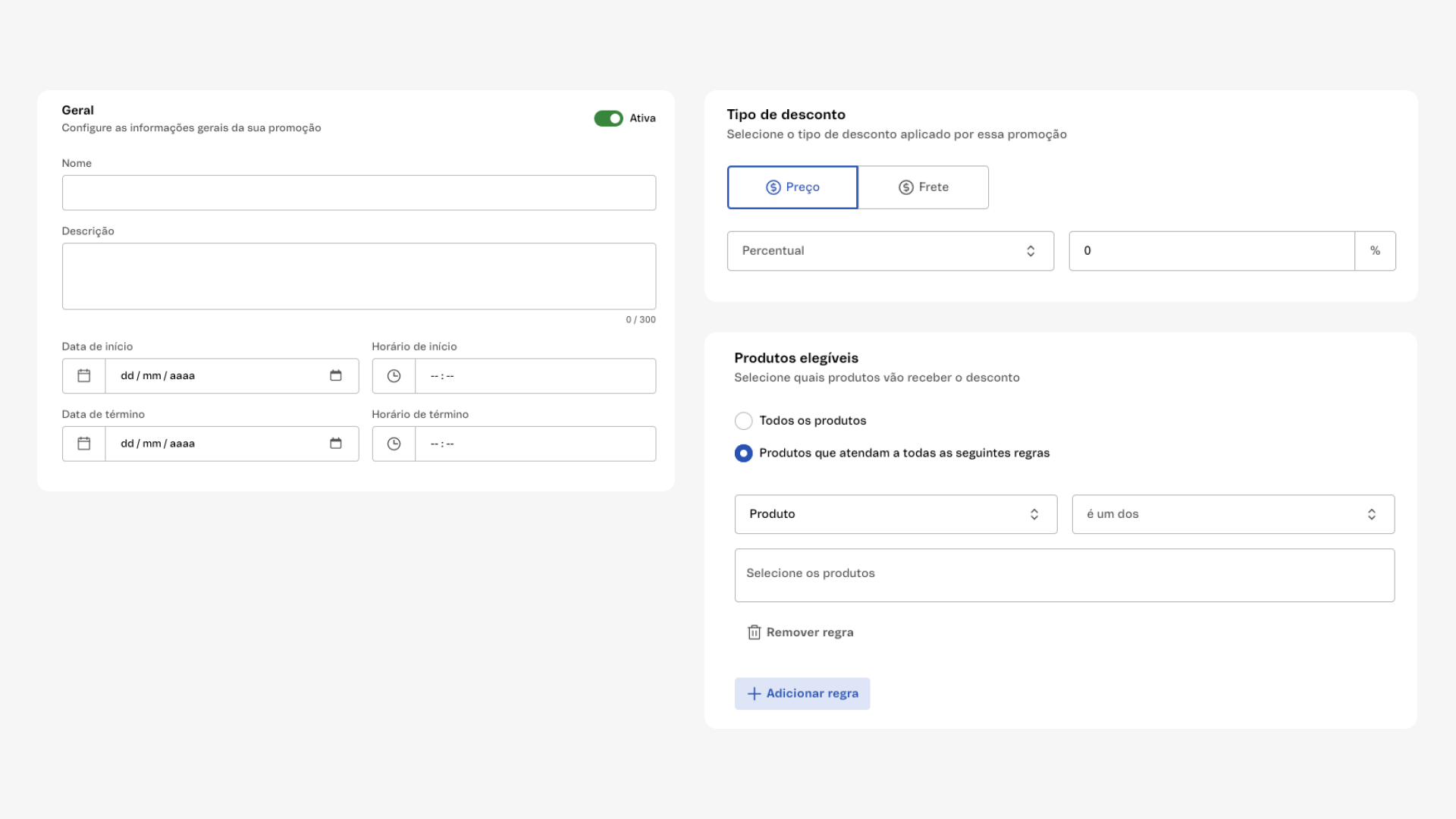
- VTEX offers no native hooks — any interception had to happen in the Sinatra layer.
- Teams are lean — any flow with more than 3 clicks would be ignored.
- We can't block at the source — we can only act after creation. That reshaped our entire approach.
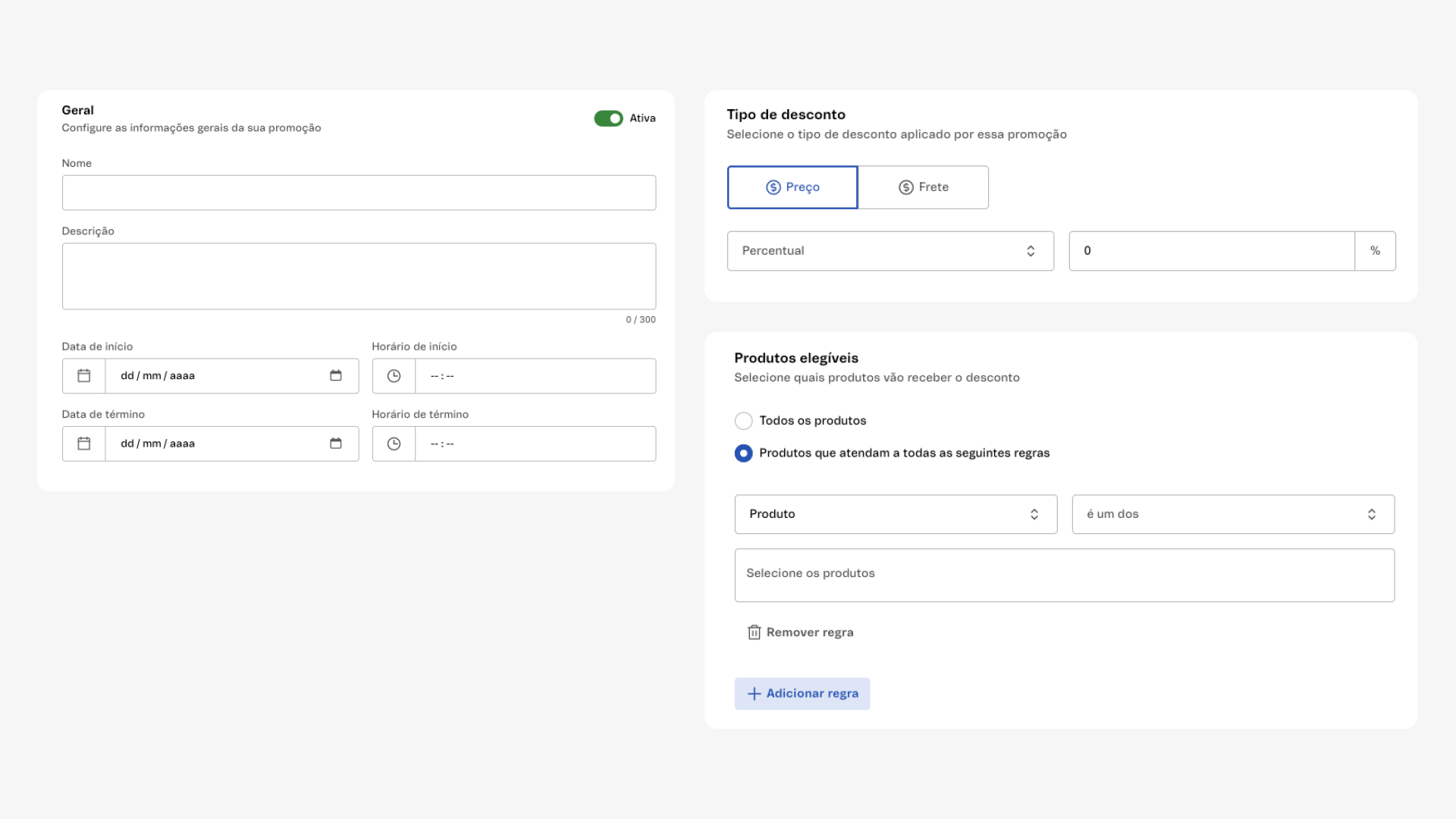
The Promotions Guardian: Pull Request + MFA applied to e-commerce.
The solution is a double-review system inspired by two well-known mechanisms MFA and Pull Requests.
The logic: no promotion created in VTEX can be activated unless two members of the team registered in Sinatra review and approve it. If one rejects, the promotion is disabled. Sinatra acts as an intermediary — it detects the created promotion, places it in a review state, and only releases it to production once the approval quorum is met.
Design analogy
| Reference | Parallel |
|---|---|
| Pull Request | No code goes to main without review. No promotion goes to prod without approval. |
| MFA | One factor isn't enough. Two independent approvers form the second factor. |
| Single veto | One rejection is enough to disable. Intentional asymmetry. |
| State | Description |
|---|---|
| Pending | Promotion detected, no reviewer has weighed in. Inactive. |
| Partial | One reviewer approved. Awaiting second. Still inactive. |
| Approved | Two approvers validated. Released to production. Approvers logged. |
| Rejected | A single veto closes the process. Promotion disabled immediately. |
Design decisions
Why two approvers?
A single approver creates the same problem we're trying to solve. Two independent approvers make collusion exponentially harder.
Why does one veto bring it all down?
Approving releases money. Rejecting protects. In security, we always favor the conservative side.
Active notification, not passive
The system doesn't wait for the reviewer to log in. The promotion comes to them — eliminating the 'nobody saw it' scenario.
Zero creation restrictions
Creating in VTEX stays free. The freedom to create remains; the freedom to publish without review does not.
Before and after the Guardian.
- ~23% of promotions hit prod with critical errors
- Audit via VTEX ticket — Up to 8 weeks to start
- 0% traceability over creators and approvers
- Review over Email, Teams etc. — no record, no accountability
- 0 promotions with errors in production (90 days)
- Real-time promotions review, approval and audit
- 100% with approver records
- 47 blocked in the 1st month — 12 potentially fraudulent
“Before, I'd find out about the problem from the client. Now I know before the client does.”
What this project leaves behind.
Governance Design is key
The Guardian isn't a security feature. It's a governance layer that changes how teams relate to their promotions.
Engineering analogies make alignment easier
Referencing Pull Requests and MFA was the single decision that accelerated internal alignment the most.
One real case is worth more than 10 decks
The internal case that motivated the project was the most powerful argument in the buy-in journey.
Platform constraints shape the right solution
Not being able to block creation in VTEX forced us into a post-creation model that's more robust. The constraint became a principle.